Using Marking Definitions
Being able to structure the handling of data through the use of data markings is vital for organizations who share cyber threat intelligence (CTI). This benefit allows STIX producers to limit the accessibility of objects and also communicates terms of use and copyright information.
Scenario
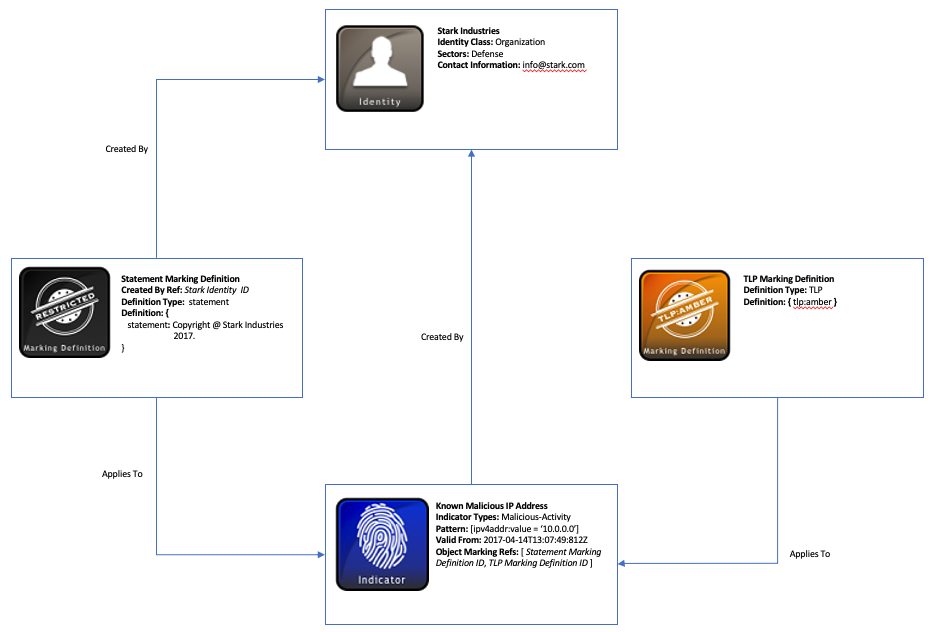
This scenario focuses on a STIX producer, “Stark Industries”, who imposes object markings on an indicator object. Before sharing this indicator, Stark creates a “Statement” marking definition and selects a “Traffic Light Protocol” (TLP) marking definition to apply to the indicator. These marking definitions incorporate copyright information and restrict the usage of the indicator based on its TLP marking type.
Data model
First, we start with the producer of the STIX content in this scenario, Stark Industries. The information relevant to this company can be represented using an Identity STIX Domain Object (SDO). Like with all STIX objects, an id attribute uniquely identifies Stark Industries and can be referenced within all the objects they generate with the created_by_ref property. Although created_by_ref is optional, this is helpful for attributing the created marking definitions directly to Stark. The Identity object is also useful for listing other relevant details about Stark such as contact_information and what type of identity they are with the identity_class field.
Next, Stark used a couple of STIX Marking Definition objects to restrict the handling of the Indicator object and to incorporate copyright information. In the first instance, Stark chose a TLP Marking Object Type to communicate appropriate restrictions for the indicator. For this Marking Definition object, the definition_type must be tlp and the definition field must contain one of the four types of TLP. In this example, the TLP restriction type is amber. This provides limited disclosure to only appropriate recipients who have a need to know. To read about this restriction and the other types of TLP, check out US-CERT’s TLP Definitions and Usage.
A second marking type created by Stark Industries called Statement, is used to represent their copyright information and is applied to all objects they produce. This is similar in format to the TLP Marking Definition object, except the definition_type in this case must be statement and there is a created_by_ref field since TLP is already pre-defined in the STIX 2.1 specification. The definition field contains any type of copyright information you want to convey. For this organization, it simply states Copyright @ Stark Industries 2017. This property could also communicate any terms of use, or you could incorporate both since Statement allows for multiple marking types.
A point of emphasis worth noting is that Marking Definition objects cannot be versioned like other STIX objects. For instance, if Stark Industries wanted to update their Statement information or add terms of use to the marking definition, they would have to generate a new Marking Definition object with the Indicator SDO updated to point to this new definition. They could not add or change their current Statement marking and simply update the modified property like with other objects, because there is no required modified property with Marking Definition objects. To understand more about versioning objects, check out this helpful tutorial video on How to Use Versioning in STIX 2.
Finally, Stark can apply these marking definitions to the Indicator SDO that contains the malicious IP address they discovered on their network. These object markings are embedded within the Indicator object in the object_marking_refs property and reference the Marking Definition object id’s for both Statement and TLP. Once referenced, these markings apply to the Indicator object. It’s worth mentioning that this property and the created_by_ref property presented earlier represent one of just a few embedded relationships in STIX 2.1. In most cases, to establish a relationship between objects in STIX, such as between an Indicator and Threat Actor SDO, you would create a Relationship STIX Relationship Object (SRO).
Other than object marking references, the rest of the Indicator object contains properties that detail information about the IP address. The pattern property, for instance, is based on the STIX patterning language and represents an IPv4 address as a comparison expression: [ipv4-addr:value = '10.0.0.0']. Stark also knows this is a nefarious IP and relays this information with the indicator_types property indicating this IP is associated with malicious-activity. Due to the fact this was a known bad IP present on their network, it is advantageous for Stark to be able to apply the appropriate TLP marking definitions to this indicator.
A diagram of this scenario below shows both the Identity and Indicator SDO’s as well as the Marking Definition objects (An interactive version can be found here):
Further Reading
To read more about the objects in this example as well as common properties and vocabularies, check out the links below:
- Common Properties
- Vocabularies
- Identity
- Indicator
- Relationship
- Marking Definitions
- Statement Object Marking Type
- TLP Object Marking Type
- STIX Patterning
Implementation
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
{
"type": "bundle",
"id": "bundle--dbe491fe-6faf-4125-b019-d8938bc0294d",
"objects": [
{
"type": "identity",
"spec_version": "2.1",
"id": "identity--611d9d41-dba5-4e13-9b29-e22488058ffc",
"created": "2017-04-14T13:07:49.812Z",
"modified": "2017-04-14T13:07:49.812Z",
"name": "Stark Industries",
"identity_class": "organization",
"sectors": [
"defense"
],
"contact_information": "info@stark.com"
},
{
"type": "indicator",
"spec_version": "2.1",
"id": "indicator--33fe3b22-0201-47cf-85d0-97c02164528d",
"created_by_ref": "identity--611d9d41-dba5-4e13-9b29-e22488058ffc",
"created": "2017-04-14T13:07:49.812Z",
"modified": "2017-04-14T13:07:49.812Z",
"name": "Known malicious IP Address",
"description": "Detected malicious activity from this address",
"indicator_types": [
"malicious-activity"
],
"pattern": "[ipv4-addr:value = '10.0.0.0']",
"pattern_type": "stix",
"valid_from": "2017-04-14T13:07:49.812Z",
"object_marking_refs": [
"marking-definition--f88d31f6-486f-44da-b317-01333bde0b82",
"marking-definition--d81f86b9-975b-4c0b-875e-810c5ad45a4f"
]
},
{
"type": "marking-definition",
"spec_version": "2.1",
"id": "marking-definition--f88d31f6-486f-44da-b317-01333bde0b82",
"created": "2017-01-20T00:00:00.000Z",
"definition_type": "tlp",
"name": "TLP:AMBER",
"definition": {
"tlp": "amber"
}
},
{
"type": "marking-definition",
"spec_version": "2.1",
"id": "marking-definition--d81f86b9-975b-4c0b-875e-810c5ad45a4f",
"created": "2017-04-14T13:07:49.812Z",
"definition_type": "statement",
"definition": {
"statement": "Copyright (c) Stark Industries 2017."
}
}
]
}
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
from stix2.v21 import (Identity, MarkingDefinition, Indicator, StatementMarking, Bundle)
identity = Identity(
id="identity--611d9d41-dba5-4e13-9b29-e22488058ffc",
created="2017-04-14T13:07:49.812Z",
modified="2017-04-14T13:07:49.812Z",
name="Stark Industries",
contact_information="info@stark.com",
identity_class="organization",
sectors=["defense"]
)
marking_def_amber = MarkingDefinition(
id="marking-definition--f88d31f6-486f-44da-b317-01333bde0b82",
created="2017-01-20T00:00:00.000Z",
definition_type="tlp",
definition={
"tlp": "amber"
}
)
marking_def_statement = MarkingDefinition(
id="marking-definition--d81f86b9-975b-4c0b-875e-810c5ad45a4f",
created="2017-04-14T13:07:49.812Z",
definition_type="statement",
definition=StatementMarking("Copyright (c) Stark Industries 2017.")
)
indicator = Indicator(
id="indicator--33fe3b22-0201-47cf-85d0-97c02164528d",
created="2017-04-14T13:07:49.812Z",
modified="2017-04-14T13:07:49.812Z",
created_by_ref="identity--611d9d41-dba5-4e13-9b29-e22488058ffc",
name="Known malicious IP Address",
description="Detected malicious activity from this address",
indicator_types=["malicious-activity"],
pattern="[ipv4-addr:value = '10.0.0.0']",
pattern_type="stix",
valid_from="2017-04-14T13:07:49.812Z",
object_marking_refs=[marking_def_amber, marking_def_statement]
)
bundle = Bundle(objects=[identity, indicator, marking_def_amber, marking_def_statement])
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
from stix2.v21 import (Bundle)
for obj in bundle.objects:
if obj == identity:
print("------------------")
print("== IDENTITY ==")
print("------------------")
print("ID: " + obj.id)
print("Created: " + str(obj.created))
print("Modified: " + str(obj.modified))
print("Name: " + obj.name)
print("Identity Class: " + obj.identity_class)
print("Contact Information: " + obj.contact_information)
print("Sectors: " + str(obj.sectors))
elif obj == indicator:
print("------------------")
print("== INDICATOR ==")
print("------------------")
print("ID: " + obj.id)
print("Created: " + str(obj.created))
print("Modified: " + str(obj.modified))
print("Created by Ref: " + obj.created_by_ref)
print("Name: " + obj.name)
print("Indicator Types: " + obj.indicator_types[0])
print("Pattern: " + obj.pattern)
print("Valid From: " + str(obj.valid_from))
print("Object Marking Refs: " + str(obj.object_marking_refs))
elif obj == marking_def_amber:
print("------------------")
print("== MARKING DEFINITION ==")
print("------------------")
print("ID: " + obj.id)
print("Created: " + str(obj.created))
print("Definition Type: " + obj.definition_type)
print("Definition: " + str(obj.definition))
elif obj == marking_def_statement:
print("------------------")
print("== MARKING DEFINITION ==")
print("------------------")
print("ID: " + obj.id)
print("Created: " + str(obj.created))
print("Definition Type: " + obj.definition_type)
print("Definition: " + str(obj.definition))